Is the same concept as the multiplexing although this is a technique that can use different mechanisms. How access control policies eg identity-based policies role-based policies rule-based policies and associated access enforcement mechanisms eg access control lists access control matrices cryptography are employed by the Company to control access between users or processes acting on behalf of users and objects eg devices files records processes.

Media Access Control What Is It And Overview Kisi
Access will be monitored when account is in use.

. Media Access Control MAC protocols establish a set of rules that govern who gets to use the shared transmission media in an efficient manner. Media Access Control Policy 10 OverviewPurpose Removable media is a well-known source of malware infections and can be tied to the loss of sensitive information. Media Access Control is the set of mechanisms and protocols through which various devices on a computing and telecommunications network agree to share a media the frequency range assigned to the system.
On any given network each device must have a unique MAC address that can be factory set when the device is manufactured or set manually. Access Control for Mobile Devices. Media Protection Policy 111.
Media access control methods act like traffic lights by permitting the smooth flow of traffic on a network and they prevent or deal with collisions. Channel partitioning FDMA frequency division multiple access TDMA time division multiple access CDMA code division multiple access Random access Contention-based Aloha CSMA CSMACD CSMACA Ethernet 80211 Contention-free Token-ring FDDI. Media access How to share a channel among different hosts.
Medium Access Control Protocols and Local Area Networks Part I. E Use only approved EPA removable digital media to store EPA data. Deploying and managing policy via Group Policy.
In some systems complete access is granted after s successful authentication of the user but most systems require more sophisticated and complex control. To overcome the media divide Native Americans need increased media ownership. They must be surrendered in accordance with DHS and TSA policies immediately upon request by an authorized TSA official or when access to TSA-controlled facilities is no longer required.
All information sent to all users. BD AC must not only enforce access control policies on data leaving the MS it must also control access to the CSs resources. 1 Only the appropriate levels of access are allowed 2 Access is granted only to authorized personnel and 3 Users access rights are limited to least privilege.
In todays common use this is a MAC address. The Removable Storage Access Control feature enables you to apply policy via Group Policy to either user or device or both. The MAC sublayer is the interface between the Physical layer and the LLC sublayer.
Media access control MAC is a sublayer of the data link layer DLL in the seven-layer OSI network reference model. Cable Modem Access. To access and use Removable Storage Access Control you must.
How access control policies eg identity-based policies role-based policies rule-based policies and associated access enforcement mechanisms eg access control lists access control matrices cryptography are employed by the Company to control access between users or processes acting on behalf of users and objects eg devices files records. At this sublayer every device is assigned an address. MEDIA ACCESS CONTROL OWNERSHIP.
Depending on the sensitivity of the data it needs to make certain that BD applications the MS and CSs have permissions to access the data that they are analyzing and deal. Local Area Networks Chapter Overview. Copper Optical.
The NASA media protection policy shall be consistent with applicable laws Executive Orders directives regulations and guidance. Repeated access attempts will be limited by locking out the user ID after not more than six attempts. NPM will work to overcome any barriers to such ownership in FCC media ownership proceedings.
The purpose of this policy is to minimize the risk of loss or exposure of sensitive information maintained by MUSA Corporation and to reduce the risk of acquiring malware infections on computers on the MUSA. This sublayer decides among competing devices on who should gain the access to the media and send data. I System accounts and access are reviewed at least monthly to ensure that.
Obstacle to perfect channel utilization Finite propagation delay means that each users knowledge of the state of the system is imperfect and thus they can not perfectly schedule. Medium Access Control Part II. Ii Activities of users with significant information system roles and responsibilities are.
In addition it will establish the responsibility eligibility and approval process for members of the University community to be given. Before you get started with Removable Storage Access Control you must confirm your Microsoft 365 subscription. Media access control methods are implemented at the data-link layer of the seven-layers Open Systems Interconnection OSI reference model.
Access control is concerned with determining the allowed activities of legitimate users mediating every attempt by a user to access a resource in the system. Ii Following insertion into or connection with a non-EPA information system security personnel shall check EPA-owned USB removable media. I The removable media shall be encrypted unless the EPA Deputy Administrator or Chief Information Officer has identified all data on the device as non-sensitive in writing.
This sublayer which depends on a physical layer is a procedure controlled by the sender in which several devices on multidrop or bus networks compete to gain access to the medium for data transfer. And advance proposals of particular relevance to the Commissions Media Ownership priorities and rulemaking including. The CSO is the agency official with authority for.
MAC is responsible for the transmission of data packets to and from the network-interface card and to and from another remotely shared channel. Authorize wireless access to the system before allowing connections. Lockout duration must be set to a minimum of 30 minutes or until an administrator enables the user ID.
Access will be enabled only during the time period needed and disabled when not in use. 165321 Media Access Control. A comprehensive access control policy will aid in providing a safe and secure learning environment for the faculty staff and students at the University of South Alabama.
TSA identification media and access control media are the property of TSA. The objective is to assure effective media protection and controls to prevent loss or unauthorized access to NASA infonnation or infonnation systems. Protect wireless access to the system by deploying strong authentication of users and devices along with strong encryption that can reduce susceptibility to threats by adversaries involving wireless technologies.

Media Access Control An Overview Sciencedirect Topics

Media Access Control Protocol An Overview Sciencedirect Topics

Media Access Control An Overview Sciencedirect Topics
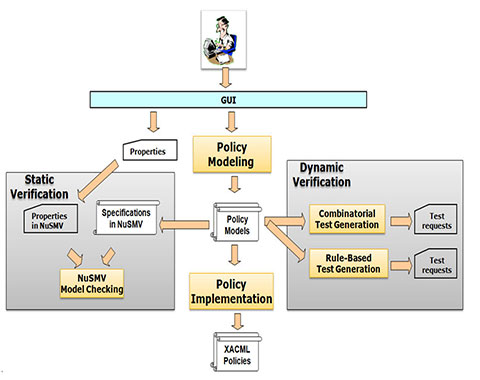
Access Control Policy Testing Csrc

Media Access Control An Overview Sciencedirect Topics

Media Access Control An Overview Sciencedirect Topics

Media Access Control An Overview Sciencedirect Topics

Media Access Control Protocol An Overview Sciencedirect Topics
0 comments
Post a Comment